RFID, or Radio-Frequency Identification, is a foundational technology in the field of Automatic Identification and Data Capture. Unlike common definitions, technically, RFID is an asymmetric wireless communication system that uses electromagnetic fields or radio waves to transmit data between an interrogation device and a response device.
This document provides insights into physical layers, modulation mechanisms, antenna techniques, environmental factors affecting signals, and practical operational efficiency analysis.
1. Physical Principles and Coupling Mechanisms
RFID's data transmission capability is based on two distinct physical principles, depending on the operating frequency and distance from the field.
Inductive Coupling - Near Field
This mechanism applies to low-frequency LF 125 kHz and high-frequency HF/NFC 13.56 MHz systems.
The near-field region is defined by the distance d < λ / 2π (where λ is the wavelength).
It operates based on Faraday's law of electromagnetic induction. The reader's antenna is a coil that generates a changing magnetic field. When an RFID tag containing a secondary coil enters this magnetic field, an induced electromotive force appears, creating a current that powers the microchip.
Data is transmitted back to the reader via the Load Variation method. The microchip on the tag switches a load resistor in parallel with the antenna, changing the mutual impedance, which causes a voltage drop at the reader's coil. The reader decodes this voltage change into binary data. Because the magnetic field decays at a rate of 1/r³, the reading range is usually limited to under 1 meter.
Backscatter Coupling - Far Field
This mechanism applies to ultra-high frequency UHF 860~960 MHz and Microwave 2.4 GHz systems.
It operates based on radar principles. The reader emits electromagnetic waves that propagate through space. The microchip on the tag changes the reflection coefficient or radar cross-section RCS of the antenna by changing the input impedance between two states. The reader detects the change in the intensity of the reflected wave to decode the data.
The power received at the tag chip follows the Friis transmission equation:
P_tag = P_reader * G_reader * G_tag * (λ / 4πd)²Where the attenuation is proportional to the square of the distance (d²), allowing operating ranges of up to 10-15 meters.
2. Antenna Theory and Wave Polarization
The performance of a UHF RFID system depends heavily on antenna design and polarization synchronization.
Linear Polarization
Electromagnetic waves oscillate on a single plane, such as horizontal or vertical.
- Advantages: Furthest reading distance due to concentrated energy.
- Disadvantages: Requires the tag antenna and reader antenna to be parallel. If the tag is perpendicular to the wave or cross-polarized, the reader will not receive a signal.
Circular Polarization
Electromagnetic waves rotate in a spiral as they travel, which can rotate right or left.
- Advantages: Can read tags in any orientation, suitable for retail environments where goods are arranged randomly.
- Disadvantages: Loses about 3dB of power (50% of energy) compared to linear polarization, resulting in a slightly shorter reading distance.
Gain and Beamwidth
- High gain (e.g. 9-12 dBi): Narrow beam, travels far. Suitable for warehouse gates, conveyor belts.
- Low gain (e.g. -20 to 3 dBi): Wide beam, near field. Suitable for smart shelves or points of sale to avoid misreading nearby tags.
3. Tag Architecture and Classification
RFID tags are technically classified based on their power source and memory structure.
Classification by Power Source
- Passive tags: No internal power source. Operates using RF wave energy. Low cost, long life.
- Semi-passive tags: Integrate a battery to power the chip and sensors, but still use backscatter to transmit information. Higher sensitivity than passive tags (-30dBm vs -18dBm).
- Active tags: Have a battery and an active wave transmitter. Reading range >100m.
EPC Gen 2 Memory Architecture
The ISO/IEC 18000-63 standard specifies 4 memory partitions:
- Reserved Memory (Bank 00): Contains a 32-bit access password and a 32-bit kill password.
- EPC Memory (Bank 01): Contains an electronic product code from 96-bit to 496-bit. This is the primary key for identification. Includes Protocol Control bits and CRC-16 error check code.
- TID Memory (Bank 10): Transponder identifier code. Contains the manufacturer code and the chip's unique serial number. This data is usually written permanently from the factory to prevent counterfeiting.
- User Memory (Bank 11): Customizable memory for users (512 bits - 8 Kbyte). Used to store additional information when there is no network connection.
4. Air Interface and Signal Modulation
From Reader to Tag
Uses amplitude modulation. Data is encoded using Pulse Interval Encoding. In this technique, the value '0' is a short pulse, '1' is a long pulse. An important feature is to always maintain wave energy in the high state for most of the bit cycle, ensuring that the tag does not lose power while receiving data.
From Tag to Reader
The tag responds weakly by changing the reflection coefficient. The encoding used is FM0 or Miller subcarrier.
- FM0: Highest speed, but susceptible to interference.
- Miller (M=2, 4, 8): Slower speed but excellent noise immunity. In environments with a lot of metal or wave interference, the reader will require the tag to switch to Miller M=4 or M=8 mode.
5. Anti-collision Algorithm
When hundreds of tags respond at the same time, signal collisions occur. The UHF Gen 2 system uses a random slotted ALOHA algorithm, also known as the Q Algorithm.
- The reader issues a
Querycommand containing the parameterQ(e.g. Q=4, equivalent to 2^4 = 16 time slots). - Each tag randomly generates a 16-bit number in the range [0, 2^Q-1].
- The tag that draws the number 0 will respond immediately.
- The reader sends an acknowledgment signal along with that random number.
- The tag sends back the full EPC code.
- If there is a collision (multiple tags draw the number 0), the reader sends a command requesting the tags to choose a different number.
6. Environmental Factors and Attenuation
Real-world RFID deployments are more complex than theory due to environmental physical phenomena.
- Multipath Fading Effect: UHF waves reflected off walls, floors, and metal create multiple paths to the antenna. These waves can interfere destructively with each other, creating dead spots in the reading area. This is why tags sometimes cannot be read even when they are very close to the antenna.
- Energy Absorption: Water and polar liquids strongly absorb UHF wave energy. The human body also causes significant signal attenuation.
- Frequency Shift: When an RFID tag is placed too close to a metal surface, parasitic capacitance changes the resonant frequency of the tag's antenna, preventing it from capturing the reader's 915 MHz wave. Specialized tags with an isolation layer should be used.
7. Security and Gen 2 V2 Standard
To counter the risks of eavesdropping and counterfeiting, the Gen 2 Version 2 standard has added security features:
- Cryptographic Authentication: Tags and readers must prove their identity via a Challenge-Response mechanism using the AES-128 algorithm. Prevents tag counterfeiting.
- Anonymity Feature: Allows tags to hide part or all of their memory, or change random responses to prevent tracking the location of the tag carrier.
- User Memory Lock: Permanently locks specific memory areas to prevent unauthorized data overwriting.
8. Middleware and Edge Processing
Raw data from the reader needs to be filtered through middleware layers according to the Application Level Event standard:
- Filtering: Removes duplicates. A tag can be read 50 times/second, the system only needs to report "Tag A has appeared".
- Smoothing: Handles tag flickering, i.e. reading well suddenly losing signal due to interference and then regaining it.
- Logical Mapping: Converts the EPC code (e.g. 303405...) to business information (e.g. Shirt size M, Shipment 123).
9. Business Factor Analysis and Operational Efficiency
Adopting RFID is not just a technical problem but also a strategy for optimizing costs and processes.
Supply Chain Optimization
- Inventory accuracy: Increase from an average of 65% (with barcodes) to over 99%. This minimizes phantom stockouts and dead stock.
- Inventory speed: Reduce inventory time by 90-95%. One employee can scan 20,000 products in one hour compared to a few hundred products using manual methods.
- Traceability: The EPC code identifies each individual product unit, allowing accurate tracking of the journey from the factory to the point of sale, supporting anti-counterfeiting and effective recall management.
ROI Investment Cost Analysis
- Tag Costs (Variable Costs): Is the largest cost factor in the long term. Passive tag prices range from 4-10 US cents depending on quantity. For low-value items, tag costs can affect profit margins.
- Infrastructure Costs (Fixed Costs): Includes fixed readers, gate antennas, handheld devices, and encoding printers.
- Integration Costs: Middleware and effort to integrate into existing ERP systems.
- Return on Investment: Businesses typically reach breakeven after 12-24 months due to labor cost savings, reduced merchandise loss, and increased sales due to merchandise always being available on the shelf.
10. Typical Practical Applications
Intelligent Transportation: Non-Stop Toll Collection System (VETC/ePass)
Purpose: Eliminate the time to stop the car to pay cash, reduce congestion at toll stations, and increase revenue transparency.
Technical Configuration:
- Identification tag (E-tag): Uses a passive UHF tag attached to the car's headlight or windshield. The tag is designed to withstand the sun and rain and prevent removal.
- Long-range reader: Installed on the gantry, using a linearly polarized antenna with a high gain (12 dBi) to focus the beam on a specific lane.
Operating Mechanism: When a vehicle enters the toll lane at a speed of 40-60 km/h, the reader activates the E-tag from a distance of 6-8 meters. The backend system authenticates the vehicle's identifier, checks the balance in the e-wallet, and deducts money automatically in less than 0.2 seconds.
Fashion Retail: Uniqlo/Decathlon Model
Purpose: Speed up checkout (Self-checkout), reduce cashier personnel, and ensure absolute inventory accuracy.
Technical Configuration:
- Integrated RFID tag: The RFID chip is embedded directly into the paper price tag (hangtag) or fabric label (care label).
- Point of Sale (POS) machine: The receiving area is a "cubby" covered with wave-shielding material (Faraday cage) to localize the signal.
Operating Mechanism: Customers place the entire basket of goods into the machine's cubby. The reader inside scans all the tags simultaneously (Batch reading) regardless of the position or orientation of the product. The data is compared with the ERP system to display the invoice.
Asset Management and Logistics
Purpose: Automate the recording of goods entering and leaving the warehouse without stopping the forklift.
Operating Mechanism: Reading portals (RFID Portal) are installed at the warehouse door (Dock door). When a forklift carrying a pallet of goods passes through, the reading portal will scan all the tags on the container and the forklift's identifier tag. The WMS system automatically updates the "Inbound" or "Outbound" status.
11. Conclusion
Modern RFID technology is a synthesis of electromagnetic field physics, low-power microcircuit engineering, probability statistics theory, and cryptography. Successful deployment requires a balance between technical factors such as frequency selection, antenna design, and business factors such as tag cost control and operational process restructuring.
Was this article helpful?
Related Articles
The Ultimate UWB Module Comparison: Prices, Specs, and Use Cases
Feb 23, 2026

Under the Hood of Amazon's Just Walk Out: An RFID Engineer's Analysis
Feb 19, 2026
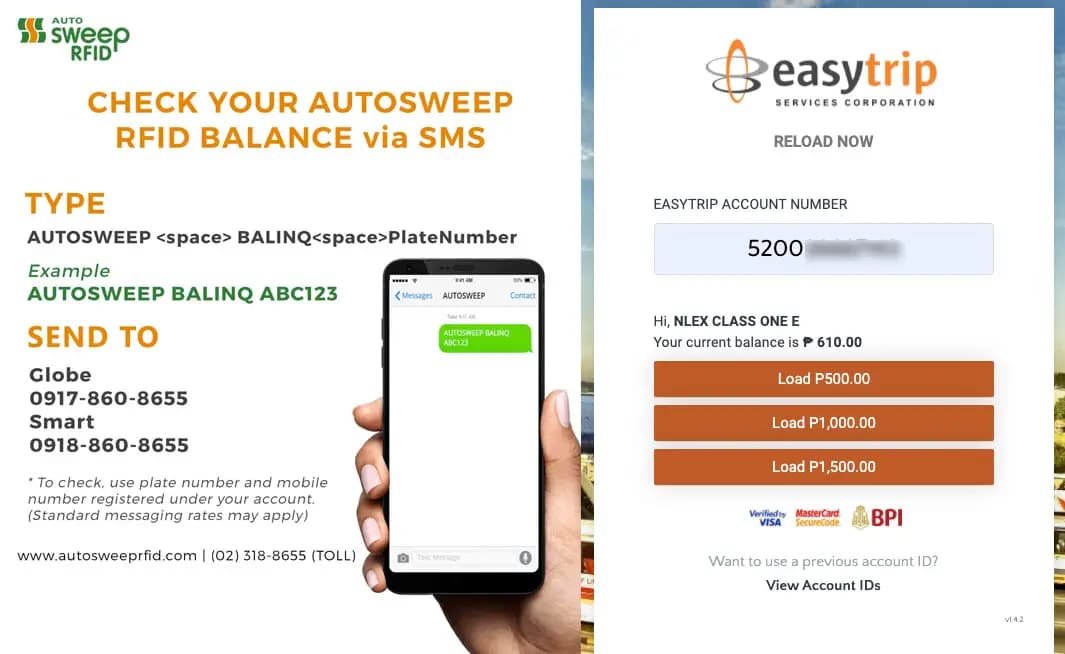
How to check Easytrip RFID Balance: The Ultimate Guide for Smart Motorists
Feb 19, 2026
Unlocking Agentic Commerce with Universal Commerce Protocol (UCP) and AI
Feb 19, 2026
